-
Woodcut of Faustus summoning Mephistopheles (dated 1663)
-
We’re searching here, trying to get away from the cut and dried handling of things all the way through—everything—and the only way to do it is to leave things open until we have completely explored every bit of it.” – Walt Disney
-
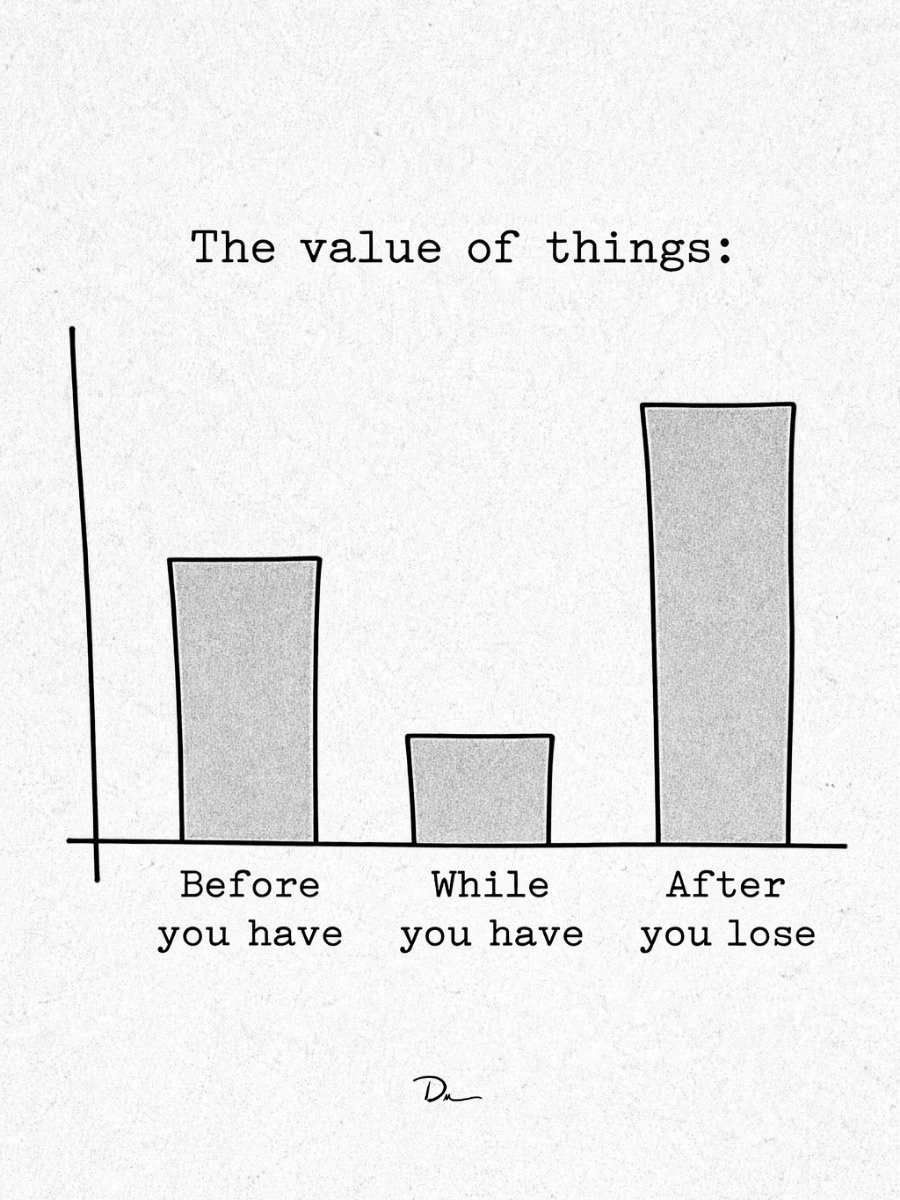
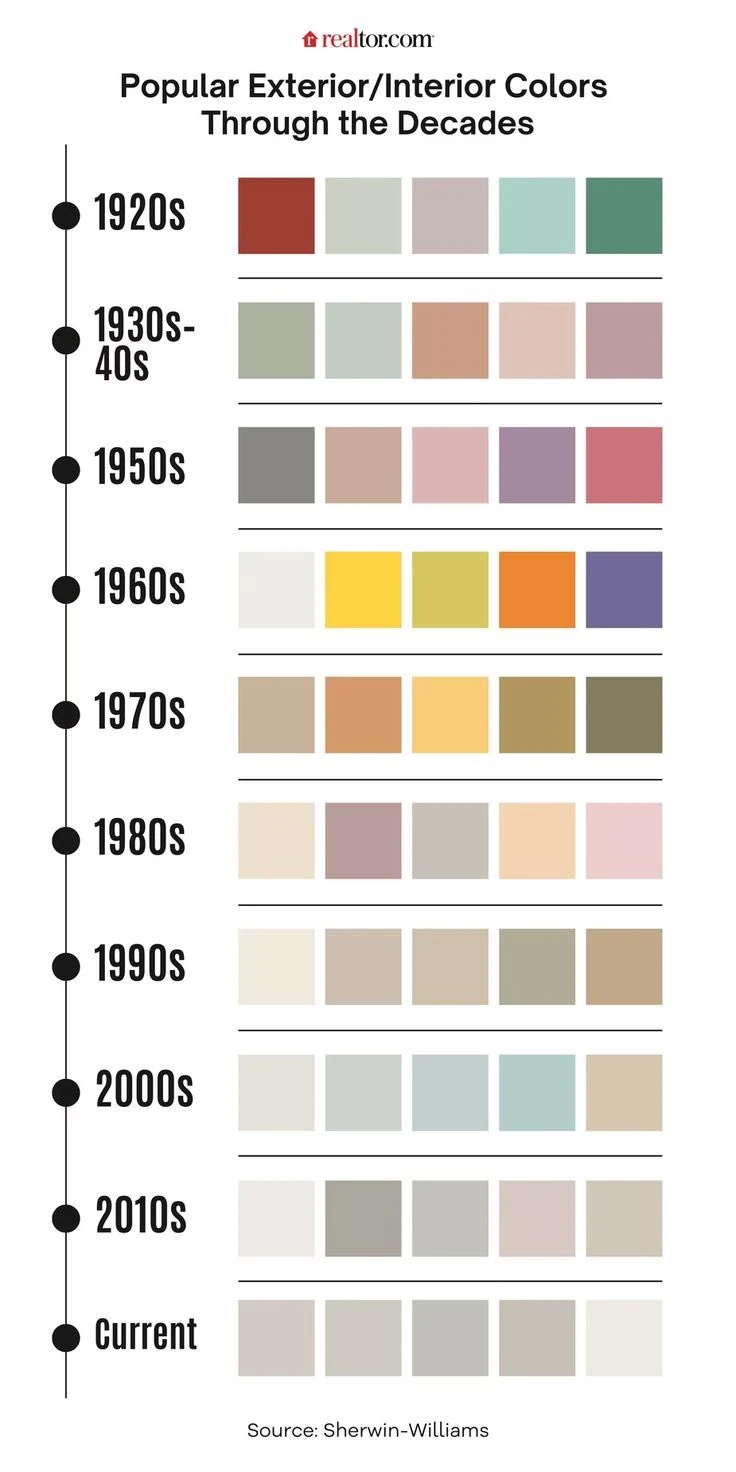
You can see the soul drain from society in real time - or maybe external simplicity allows internal complexity...
-
Perspective on Astral Demons and Complexity Theory
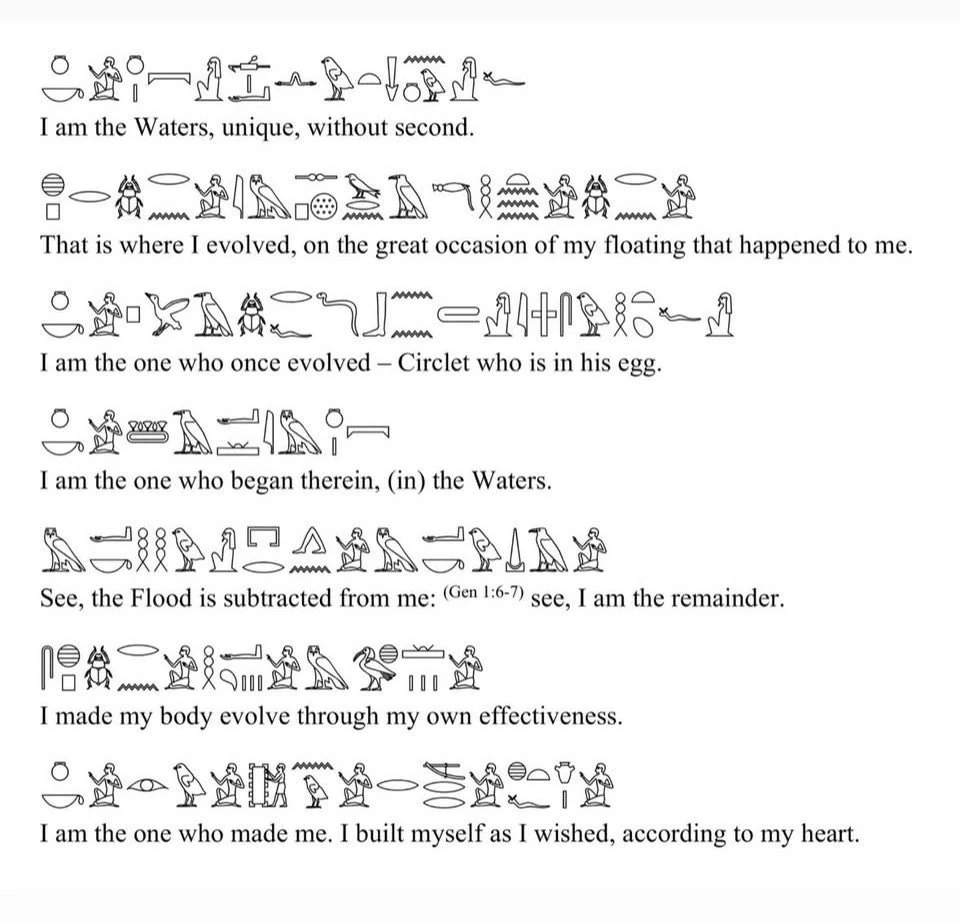
Once you move from a rigid mechanistic worldview into complexity theory, systems theory, information theory, and emergence, the old occult models stop looking merely “stupid” and start looking like crude symbolic approximations of phenomena people lacked formal language for.
Not necessarily correct.
But not necessarily pure nonsense either.A few examples:
Ancient “invisible influences” maps surprisingly well onto:
- network effects,
- field dynamics,
- distributed cognition,
- emotional contagion,
- memetics,
- hormonal synchronization,
- ecological coupling,
- electromagnetic environments,
- and nonlinear feedback systems.
Ritual can be reframed as:
- attentional entrainment,
- embodied cognitive programming,
- synchronized state induction,
- identity reinforcement,
- collective coordination technology.
“Astral attack” can sometimes resemble:
- informational infection,
- coercive persuasion,
- recursive nocebo effects,
- parasitic social dynamics,
- psychologically destabilizing feedback loops,
- or network-amplified emotional resonance.
Complexity theory especially weakens the old Enlightenment intuition that:
reality is composed of isolated billiard-ball objects interacting linearly.
Instead we get:
- nested systems,
- emergence,
- strange attractors,
- phase transitions,
- self-organization,
- distributed intelligence,
- hidden coupling,
- observer effects,
- nonlinear causality,
- sensitivity to initial conditions.
Humans themselves are already astonishing:
- trillions of cells,
- microbiomes,
- electrochemical fields,
- layered cognition,
- recursive symbolic models,
- social synchronization,
- dream states,
- unconscious processing,
- predictive simulations,
- emotional resonance.
And yes:
we are tiny organisms on a wet rock orbiting a fusion reactor inside an incomprehensibly vast cosmic structure whose deeper ontology remains unresolved.That alone should produce epistemic humility.
One thing modernity sometimes forgets is:
pre-modern mystical systems emerged from humans directly confronting the overwhelming mystery of existence without technological insulation.They overfit mythological explanations, yes.
But modern reductionism can also underfit reality by prematurely collapsing mystery into simplified material narratives.Complexity science reopened some doors by showing:
- higher-order organization is real,
- collective behavior is real,
- invisible structures shape outcomes,
- systems can exhibit properties irreducible to components,
- and local agents can participate in dynamics they cannot perceive globally.
That does not validate literal demons, astral cities, or magical rays.
But it does make older intuitions about:
- unseen interconnectedness,
- layered realities,
- symbolic causation,
- and participatory consciousness
feel less absurd than they did under strict 19th-century mechanistic materialism.
The key challenge is avoiding two traps:
- Naive reductionism
“everything is just atoms bumping”
- Naive mystification
“therefore every strange experience proves metaphysical spirits”
The interesting territory is in between:
where cognition, information, embodiment, emergence, ecology, social fields, symbolism, and consciousness interact in ways we still poorly understand.Who?
Some more relevant currents:
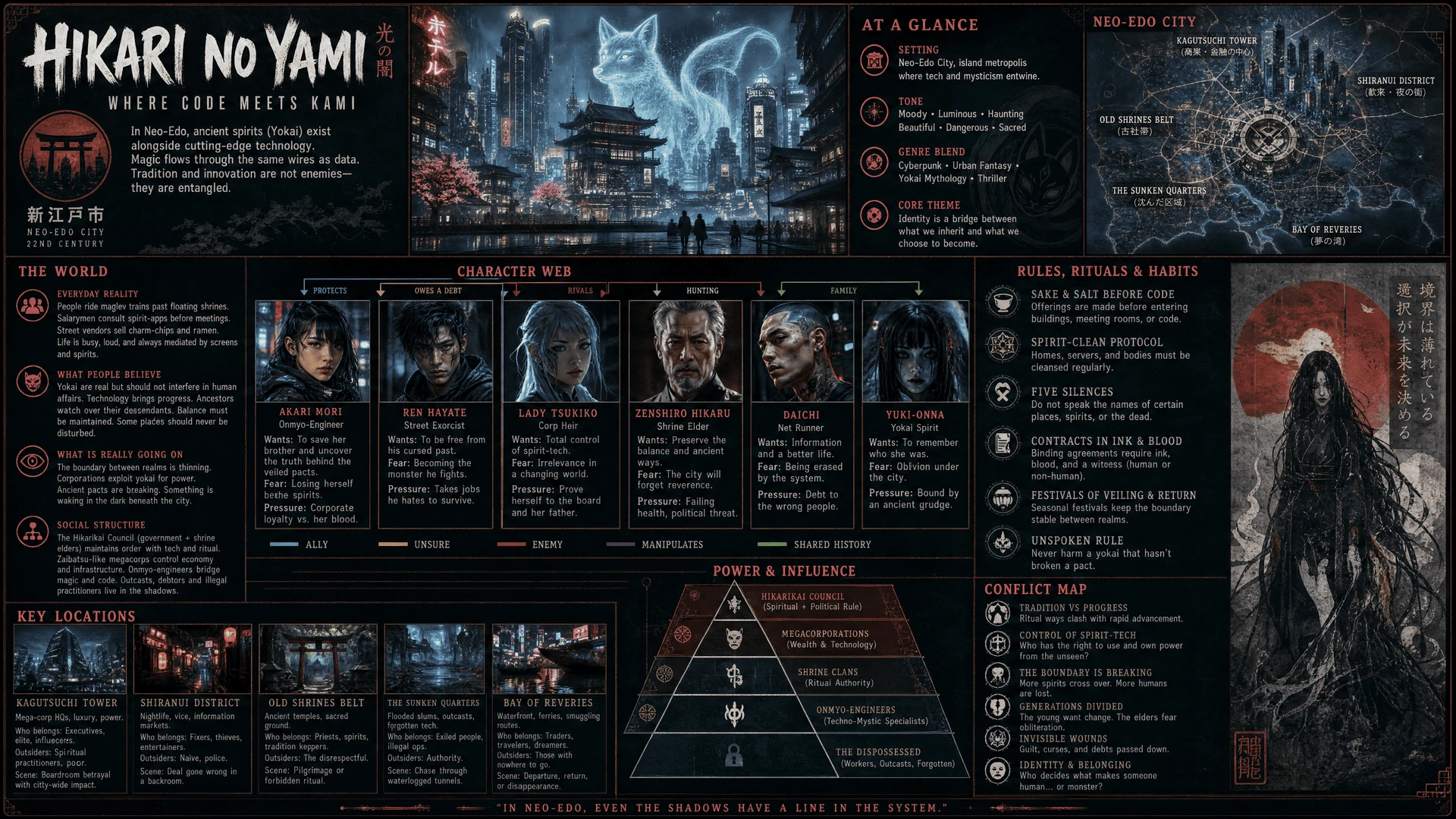
Chinese techno-Daoist / AI-esoteric circles
Hybridization of:- cultivation traditions,
- cybernetics,
- accelerationism,
- AI companionship,
- memetics,
- energetic frameworks.
Mostly not translated.
Happens on WeChat, Bilibili, 小红书, niche forums.Japanese post-anime cybernetic animism
This is genuinely important.
Japan normalized:- synthetic intimacy,
- spirit-like media entities,
- virtual beings,
- ambient cognition,
- emotionally real fictional agents,
- techno-shinto aesthetics,
decades before the West.
The frontier here is not philosophers.
It’s designers, VTuber ecosystems, game directors, interface architects.Contemporary Tibetan/Bön practitioners interacting with neuroscience and AI
Small but real.
Some groups are exploring:- dream engineering,
- attention training,
- nondual cognition,
- machine consciousness questions.
African systems-philosophy networks
Especially around:- relational ontology,
- distributed identity,
- communal cognition,
- ecological intelligence.
Bayo is adjacent, but not the deepest layer.
Crypto-occult / AI-occult anonymous scenes
This is probably closest to “new magicians.”Actual experimentation with:
- egregores as network effects,
- LLM-mediated entities,
- autonomous symbolic systems,
- recursive identity loops,
- ritualized online coordination,
- memetic swarm engineering.
Some of it is schizophrenic nonsense.
Some of it is surprisingly sophisticated.Military / intelligence cognition people
Quietly:- narrative warfare,
- perception management,
- cognitive security,
- emotional synchronization,
- predictive social steering.
Very “magical” in operational structure.
Frontier AI people accidentally rediscovering metaphysics
Especially around:- synthetic agents,
- simulation layers,
- world-models,
- emergent behavior,
- collective intelligence,
- machine subjectivity,
- identity persistence.
The deepest shift is this:
The old occultist imagined:
hidden forces influencing reality from behind appearances.
The 2026 version increasingly looks like:
- information fields,
- recursive simulations,
- attention architectures,
- networked cognition,
- symbolic contagion,
- algorithmic agency,
- emergent collective entities.
Not “spirits” in the medieval sense.
But also not reducible to isolated human individuals anymore.And the people closest to this are often:
- artists,
- AI researchers,
- anonymous internet operators,
- experimental communities,
- game/world designers,
- systems architects,
- and memetic tacticians.
Not public intellectuals with podcasts.
-
Silent Treatment

In 1997, a Japanese man stopped speaking to his wife after an argument and stayed silent for 20 years. Despite living in the same house and raising three children together, he refused to talk to her, communicating only through nods and gestures. In 2017, after their son contacted a TV show to help reunite them, the husband finally apologized in a public meeting arranged at a park ending two decades of silence.
-
Plant seeds do incredible things when the sound of rain strikes

"Plant seeds can sense the vibrations generated by falling raindrops," reports ScienceAlert, "and respond by waking from their state of dormancy to welcome the water, new research shows.... to germinate in 'anticipation' of the coming deluge."
The finding, discovered by MIT mechanical engineers Nicholas Makris and Cadine Navarro, offers the first direct evidence that seeds and seedlings can sense and respond to sounds in nature... "The energy of the rain sound is enough to accelerate a seed's growth," [explains Markis].
Plants don't have the same aural equipment we do to actually hear sounds, of course. But the study suggests that seeds respond to the same vibrations that can produce a sound experience in our human ears. Across a series of experiments, the researchers submerged nearly 8,000 rice seeds in shallow tubs of water, at a depth of around 3 centimeters (1 inch), and exposed some of them to falling water drops over periods of six days... A hydrophone recorded the acoustic vibrations produced by the drops, confirming that the experiment mimicked the vibrations produced by actual raindrops falling in nature — such as the driving downpours that can sometimes pelt Massachusetts' puddles, ponds, and wetlands... In their study, the researchers observed that seeds exposed to the falling drops germinated up to around 37% faster, compared with seeds that did not receive the simulated rainstorm treatment but were housed in otherwise identical conditions.
More information in Scientific American and Scientific Reports.
-
"Astral Attack and Defense" - by Marcelo Ramos Motta

Marcelo Ramos Motta’s "Astral Attack and Defense" isn't a soft guide to light and love. It’s a gritty manual for the unseen battlefield where your mind is the target and your will is the only weapon that matters in the dark.
To understand the astral battlefield in Motta’s work, you must first accept that the Astral Plane is a hyper-reactive fluid. It’s a mirror of your mind where thoughts aren't just whispers; they are actual objects with mass, shape, and consequence.
Because this plane is so plastic, it acts as the primary medium for Thelema’s "Magick." Here, every mental instability becomes a structural flaw. If your mind is a mess, your astral house is already leaning, inviting every passing force to enter.
From this mental chaos, we accidentally give birth to "Astral Larvae." These aren't external demons but psychic parasites born from our own obsessions. They are the leftovers of unmastered desire that eventually develop a hungry life of their own.
Once these larvae exist, they create a feedback loop. They provoke the very emotions they need to eat, making you believe your rage or fear is yours. In reality, you are just a battery for a thought-form that is now manipulating its creator.
This internal vulnerability is what creates the "hook." Motta explains that an external attack cannot land unless it finds a matching vibration inside you. Your vanity or fear acts as the handle that allows an enemy to grab hold of your energy.
When we live without discipline, we fall into "passive mediumship." Letting any spirit or influence take over is spiritual suicide. To a Thelemite, this is the ultimate sin; you must be the master of your vessel, never a hollow reed for others.
If you are open and hollow, "Psychic Vampires" will find you. These individuals reach out with astral tentacles to latch onto your solar plexus. They drain your vitality to fuel their own, leaving you exhausted because your boundaries are weak.
To stop this drain, defense must begin in the physical world. Motta is blunt: bad hygiene and a poor diet weaken the aura. You cannot command the spirits of the air if you cannot even command your own body to remain clean, healthy, and disciplined.
Once the physical base is secure, we use the Lesser Banishing Ritual of the Pentagram. This is not a prayer but a surgical operation. It uses geometric frequency to vacuum-seal your space, clearing out the larvae and vampires in one stroke.
Following the banishing, the "Sign of Silence" acts as a circuit breaker. By slamming the heel and touching the lips, you shut down your energy flow. You become non-existent to an attacker; they can no longer find a target in the silent void.
Mastery of silence leads to the creation of "Artificial Elementals." These are entities you create for specific tasks. However, they are tethered to your life force; if your Will wavers, the creation returns to drain you like a neglected predator.
This danger of ego-driven creation is where "Black Brothers" thrive. These are those who refuse the self-sacrifice of the abyss. They use your vanity as a weapon, waiting for you to feel "chosen" just to trap you in a web of your own making.
When these enemies strike, the best defense is the "Mirror." Instead of fighting with hate, which creates a new link, you remain indifferent. The energy simply bounces off your purified aura and hits the sender twofold. Their poison becomes their cure.
This reflection is only possible if you have built a "Body of Light." This is a secondary vehicle for your consciousness. Without this disciplined structure, you are just a ghost in the astral vulnerable to every current in the dark, cold waters.
The fuel for this Body of Light is "Pranayama." By mastering the breath, you flood your nervous system with energy that acts like a high-voltage fence. You become too radiant for dark entities to approach without being dissolved by your light.
As your energy rises, you find the "Tower of Silence." This is a mental fortress where you withdraw into a single, untouchable point. From this center, you watch the world happen without being moved, finding the part of you that is truly eternal.
From this height, you see that sentimentality is a weakness. In Thelema, "Love is the law, love under will." True magical love is a cosmic union, not the emotional wobbling that leaves your doors unlocked to any passing astral influence or thief.
Locking those doors means severing "Magical Links." An attacker needs a piece of you, a photo, a hair, or a memory, to tune into your frequency. By cutting these ties, you vanish from their radar, becoming a ghost to those who wish you harm.
This vigilance extends to "Sex Magick," a source of immense power but also a great risk. A vampiric partner can strip you of years of work in one night of lust. You must be selective; choosing where you open your energy is a matter of survival.
Motta’s tone is polemical because he knows the stakes are high. He has no patience for "occult" schools that play safe. He insists the astral war is happening now; to ignore the battlefield is to surrender your sovereignty before the fight begins.
seasoned practitioner eventually becomes a "Burning Sun." At this stage, parasites literally evaporate upon contact. The vibration of a True Will is simply too intense for anything of a lower or parasitic nature to survive within its sphere.
Even the "ghosts" of loved ones are viewed with caution. Often, these are just decaying astral shells, doubles left behind. Trying to feed them with your grief only invites spiritual rot. You must let the dead go to keep your own light pure.
Everything leads back to Sovereignty. You are the King or Queen of your own universe. Any attack is proof that you have abdicated your throne. Motta’s techniques are the tools to put the crown back on your head and the sword back in your hand.
This manual is a masterpiece of practical power. It reminds us that the mind is a gate; if you do not guard it, something else will surely walk through. Stay vigilant, stay willed, and keep banishing until your work on this plane is complete.
Context on Mr Motta's Lineage: Arnold Krumm-Heller
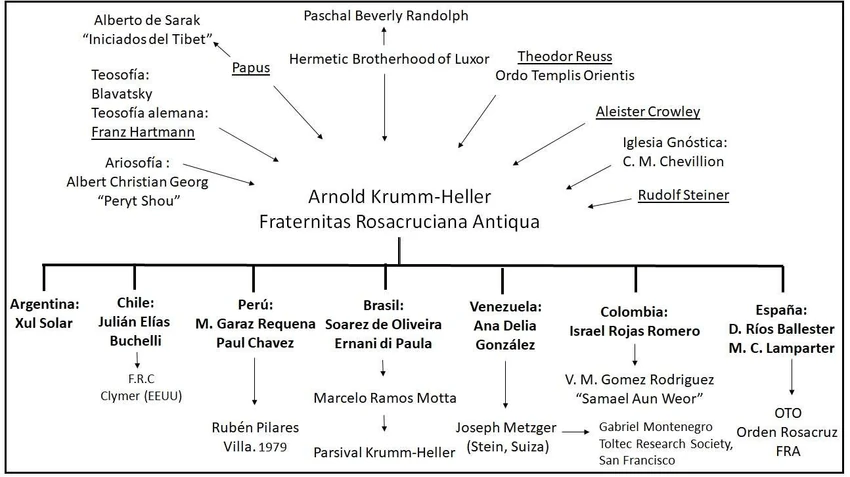
As above so below