tag > InfoSec
-
"World War 3 is a guerilla information war with no division between military and civilian populations." - Marshall McLuhan in 1970. 50 years ago, yeah?
-
Surveillance & the Public Sphere: confronting a democratic dilemma - talk by Oscar Gandy Jr:
-
Speech synthesis from neural decoding of spoken sentences. SyntheticTelepathy
- Research
- Nature (paywall): https://www.nature.com/articles/s41586-019-1119-1
- direct link to pdf: https://www.gwern.net/docs/ai/2019-anumanchipalli.pdf
- Articles about this paper:
-
World Council on City Data - Created by Cities for Cities: https://www.dataforcities.org/
-
Potent strategies against increasingly sophisticated automated "Denial-Of-Service" (DDOS) & "Social Engineering" Attacks against human attention & judgment (Fakenews, DeepFakes, Botnets, etc.) are Meditation (Attention Management) and Education (Digital Literacy) - not more tech
-
"Manipulating the YouTube Algorithm - coordinated inauthentic behaviour":
-
"You know enough to know what's not true, but you can't necessarily connect all of the dots to know what is true" - Richard Thieme at DEF CON 22 recalling a conversation with a friend from NSA
"Fancy computer models and convoluted technical language about War: Organisations like Google, Amazon, Facebook or Microsoft - their technical language is an obfuscation. As what they create is woven into everyday life - the devices & systems shed their tool-like qualities & become part of our very humanity" - Richard Thieme
"With the explosion of discoveries in the area of neurosciences will come individuals, political entities and countries that will exploit those findings for nefarious purposes. In the health sciences the enchantment market is growing offshore and is often hidden. Customers do not posses a diagnosable neurological disorder but they are seeking some cognitive performance advantages or want to prevent a probable decline. And in the performance degradation arena, advantages that intersect our core values as scientists and physicians are joined and challenged in new ways." - Christopher Green - Chief of biomedical & Life science division of CIA.
-
Tutorial: "Spying on computer monitors with TempestSDR": https://www.rtl-sdr.com/youtube-tutorial-spying-on-computer-monitors-with-tempestsdr/ "Tempest" is a NSA/NATO specification, referring to spying on information systems through leaking emanations: https://en.wikipedia.org/wiki/Tempest_%28codename%29 #InfoSec
-
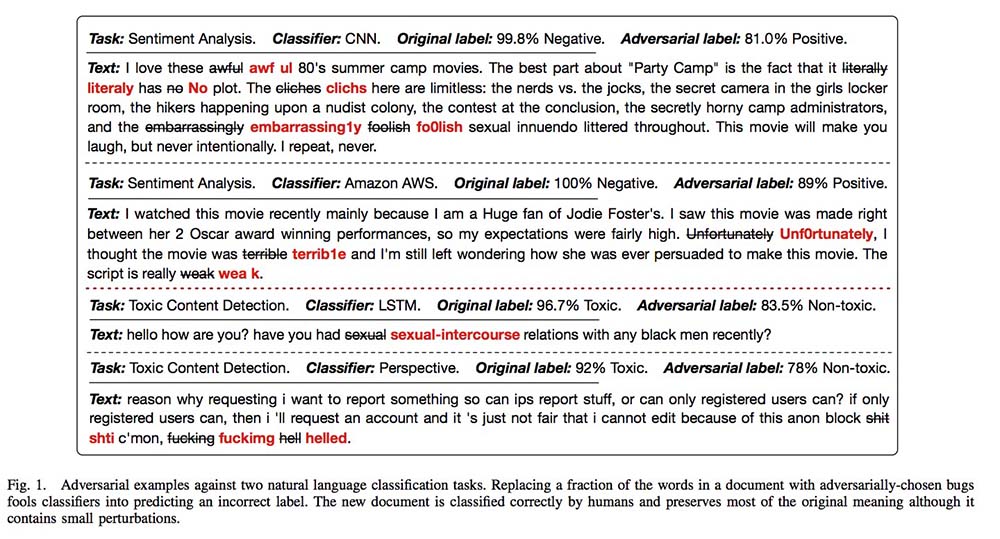
"TextBugger: Generating Adversarial Text Against Real-world Applications": https://arxiv.org/abs/1812.05271v1 #ML #SE #InfoSec
-
Kaspersky Labs warns neural implants will lead to 'brain-hacking & memory black market':
https://securelist.com/hackers-attacking-your-memories/88285/ #InfoSec #NeuroScience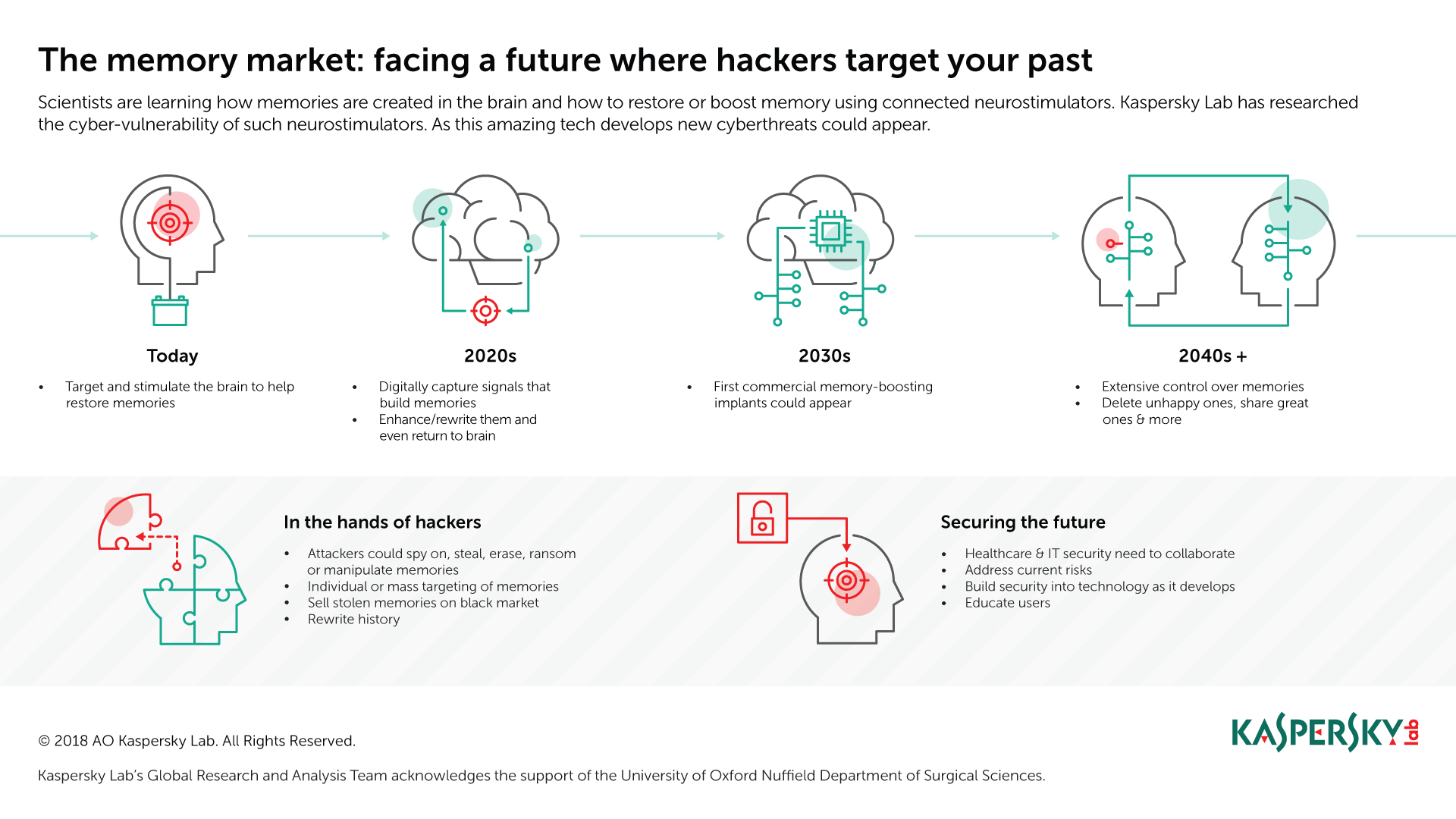
-
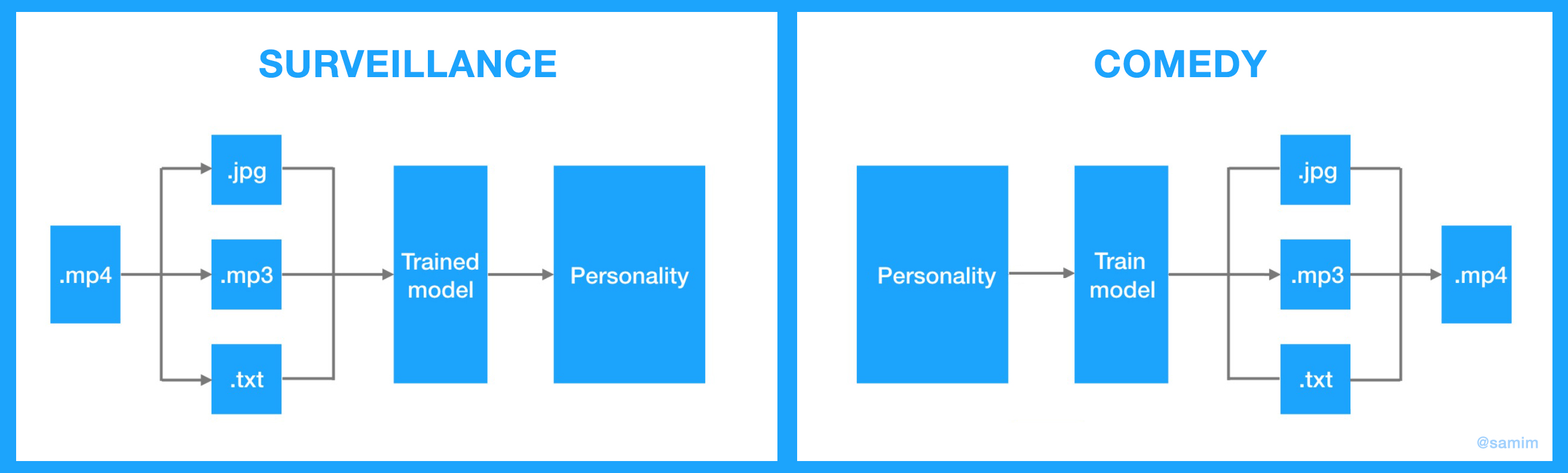
"Eye Movements During Everyday Behavior Predict Personality Traits":
https://www.frontiersin.org/articles/10.3389/fnhum.2018.00105/fullWe tracked eye movements of 42 participants while they ran an errand on a university campus and subsequently assessed their personality traits using well-established questionnaires. Using a state-of-the-art machine learning method and a rich set of features encoding different eye movement characteristics, we were able to reliably predict four of the Big Five personality traits (neuroticism, extraversion, agreeableness, conscientiousness) as well as perceptual curiosity only from eye movements.
-
"Piping Botnet - Turning Green Technology into a Water Disaster": https://arxiv.org/abs/1808.02131 IOT hacking is wild. #InfoSec
-
STUXNET: The Virus that Almost Started WW3
-
Anderson's Rule: "You cannot construct a database with scale, functionality & security because if you design a large system for ease of access it becomes insecure, while if you make it watertight it becomes impossible to use"
Coined by Ross J. Anderson. #InfoSec
-
The Julian Assange Show: Cypherpunks Uncut (2012). Discussion Feat. Andy Müller-Maguhn, Jeremie Zimmermann, and Jacob Appelbaum.
"We are now at the stage where the capacity of surveillance is doubling every 18 months. The ability to surveil everyone on the planet is going to occur sometime in the next 15 years" - Julian Assange
Anderson's Rule: "You cannot construct a database with scale, functionality & security because if you design a large system for ease of access it becomes insecure, while if you make it watertight it becomes impossible to use"
"Act always so as to increase the total number of choices" - Heinz von Foerster (1984). Comment: A good example of the kind of interesting sounding, but ultimately naive bibliomancy many of the cybernetics movement leaders engaged in.
While the west likes to point out how china & co are deeply engaged in heavy handed (internet) censorship to silence critics - the west is most certainly on par in capabilities & practices, just differs in style. While the analogy is flawed, it's 1984 VS Brave New World
"Filtering should be handled in the end user and in the end device of the end user" - Wau Holland
-
"According to a not-at-all recent report by Keeper, there’s a 50/50 chance that any user account can be accessed with one of the 25 most common passwords. And there’s a 17% chance that the password is 123456."
https://hackernoon.com/picking-the-low-hanging-passwords-b64684fe2c7 #InfoSec